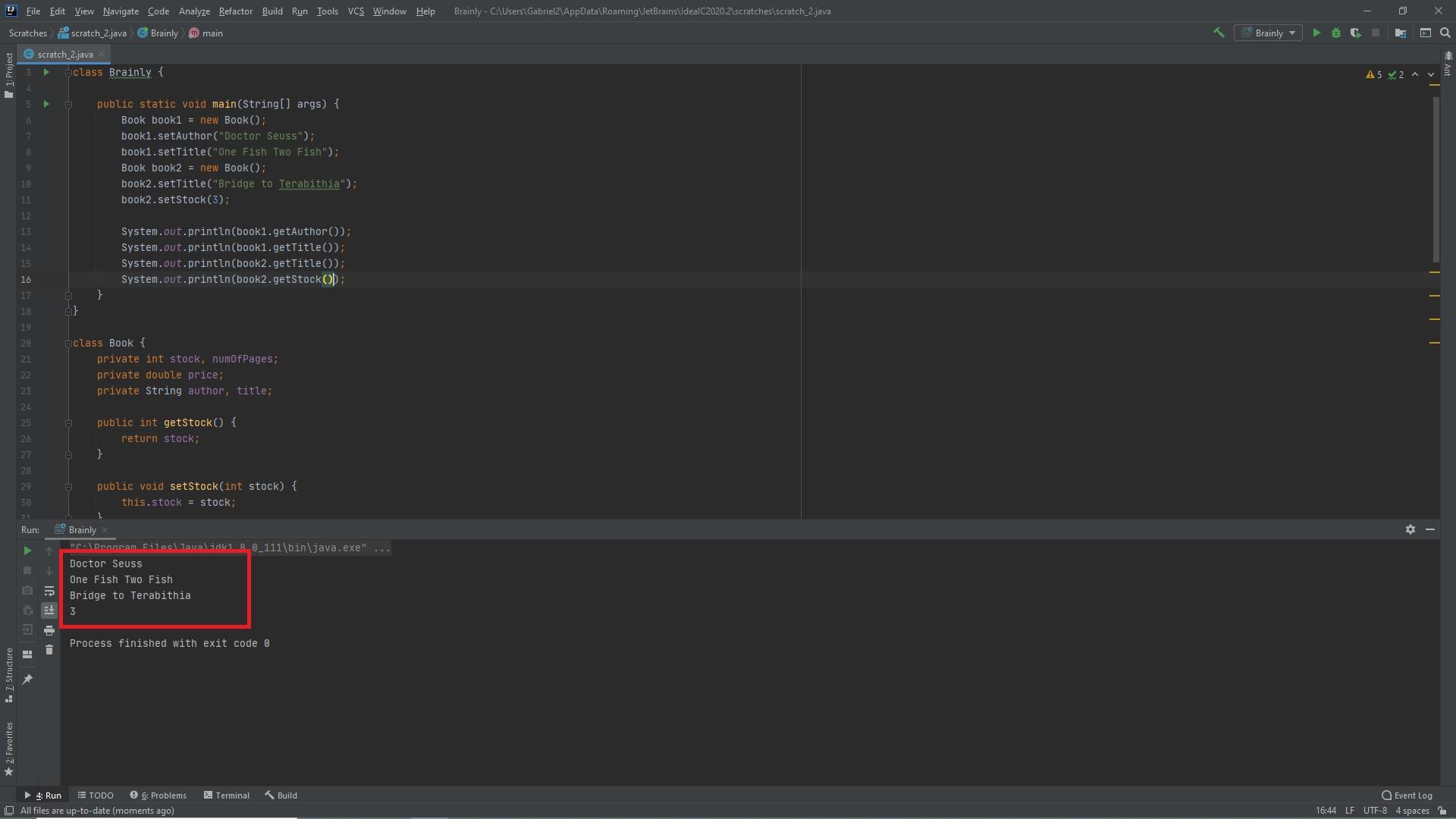
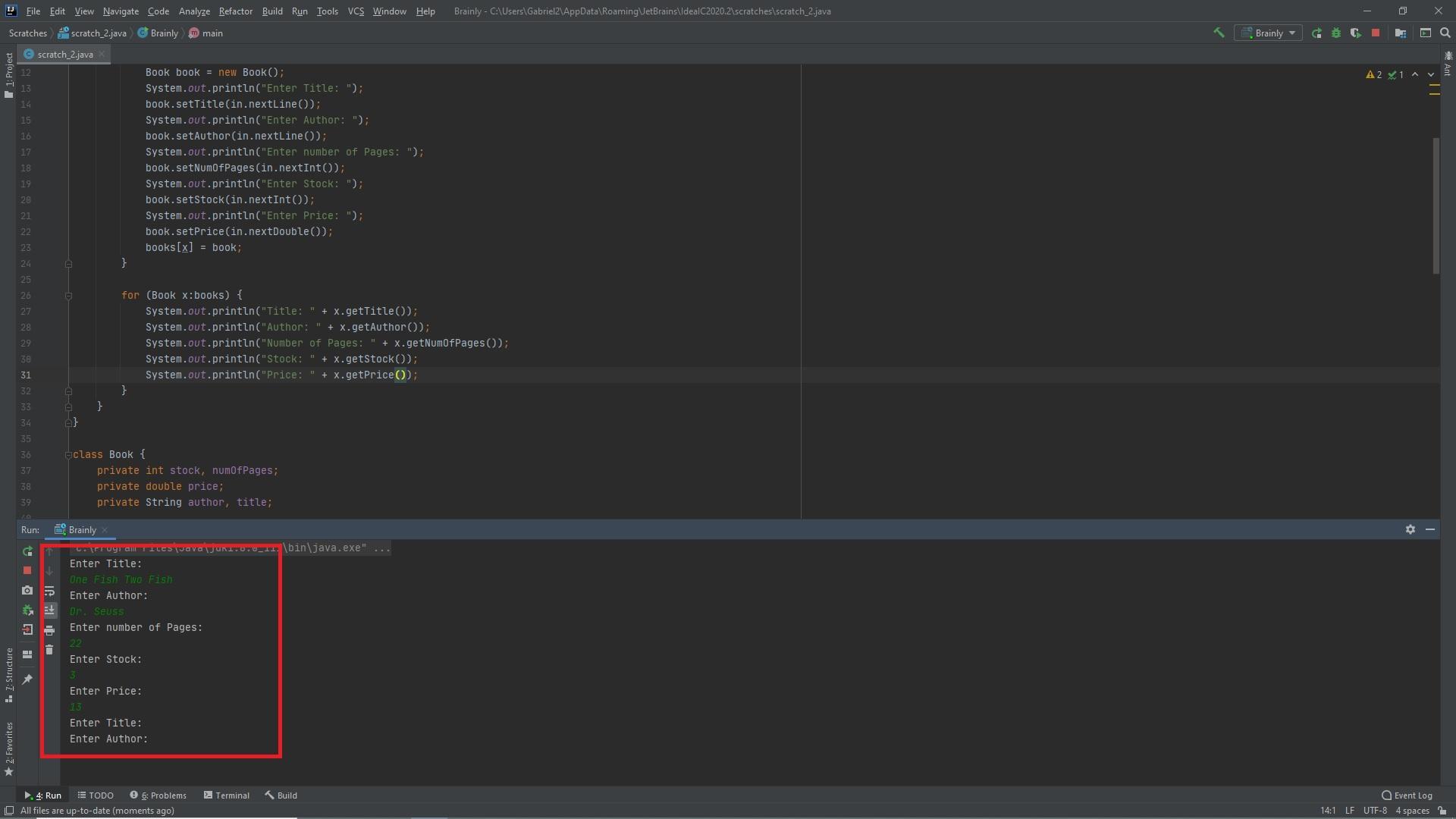
Please Complete in Java a. Create a class named Book that has 5 fields variables: a stock number, author, title, price, and number of pages for a book. For each field variable create methods to get and set methods. b. Design an application that declares two Book objects. For each object set 2 field variables and print 2 field values. c. Design an application that declares an array of 10 Books. Prompt the user to set all field variables for each Book object in the array, and then print all the values.
Answers
Answer:
Explanation:
The following code is written in Java. I created both versions of the program that was described in the question. The outputs can be seen in the attached images below. Both versions are attached as txt files below as well.
Related Questions
ghggggggggggggghbbbbbjhhhhhhhh
Answers
Answer:
Something wrong?
Explanation:
1.
A unique characteristic of the sports industry is that it seeks to attract markets that will
perform which action?
A. Demand mostly tangible products
B. Have consumers with artistic talent
c. include spectators and participants
D. Are concerned with environmental issues
Answers
Answer:
D. Are concerned with environmental issues is the answer
How do u and justify a document
Answers
Write a test program that prompts the user to enter the number of the items and weight for each item and the weight capacity of the bag, and displays the maximum total weight of the items that can be placed in the bag. Here is a sample run:
Answers
Answer:
The program in Python is as follows:
n = int(input("Number of weights: "))
weights= []
for i in range(n):
inp = float(input("Weight: "))
weights.append(inp)
capacity = float(input("Capacity: "))
possible_weights = []
for i in range(n):
for j in range(i,n):
if capacity >= weights[i] + weights[j]:
possible_weights.append(weights[i] + weights[j])
print("Maximum capacity is: ",max(possible_weights))
Explanation:
This gets the number of weights from the user
n = int(input("Number of weights: "))
This initializes the weights (as a list)
weights= []
This iteration gets all weights from the user
for i in range(n):
inp = float(input("Weight: "))
weights.append(inp)
This gets the weight capacity
capacity = float(input("Capacity: "))
This initializes the possible weights capacity (as a list)
possible_weights = []
This iterates through the weights list
for i in range(n):
for j in range(i,n):
This gets all possible weights that can be carried by the bag
if capacity >= weights[i] + weights[j]:
possible_weights.append(weights[i] + weights[j])
This prints the maximum of all possible weights
print("Maximum capacity is: ",max(possible_weights))
Write an algorithm and flowchart to display H.C.F and L.C.M of given to numbers.
Answers
Answer:
Write an algorithm to input a natural number, n, and calculate the odd numbers equal or less than n. ... Design an algorithm and flowchart to input fifty numbers and calculate their sum. Algorithm: Step1: Start Step2: Initialize the count variable to zero Step3: Initialize the sum variable to zero Step4: Read a number say x Step 5: Add 1 to the number in the count variable Step6: Add the ..
Explanation:
The project downloaded contains a package (folder) named Q1 within the src folder. Inside Q1 is a Java class named Questions. The purpose of Question 1 is to examine your understanding of loops and branching conditions. You should implement all of your code for this question in the main method of the Questioni class. While significant detail is provided below to be sure you undertand what is required, please note that the amount of code required to solve this question (Parts a-c) is less than 10 lines (total). In the Question1 class, you are given a line of code that generates a random number between 0 and 1. Math.random(): //generates number between 0 and 1 val
You are to create a loop which, in each iteration, generates a new random value, assigns it to val using the line provided and checks to see if that val is greater than 0.5. If val is greater than 0.5, a variable named counter should be incremented. The loop should continue this process (generate random value, check if it is greater than 0.5) until a total of three random numbers generated are greater than 0.5 (values do not have to be consecutive). You should also use the variable named numIterations, which is included for you, to track how many iterations of your loop were required for you to generate three random numbers greater than 0.5. A printin() statement is included for you that displays the value of numlterations. As an example of how the program should behave, if the following sequence of random numbers are randomly generated from your loop
0.3, 0.7,0.2, 0.6,0.9
then numIterations would equal 5 (the third value greater than 0.5 occured on the fifth iteration).
If
0.6, 0.8, 0.75
was the random sequence of numbers generated by your loop, then numlterations would equal 3 (the third value greater than 0.5 occured on the third iteration).
These are two examples to illustrate the scenario given in Question 1. Since at each iteration of your loop the number generated is random, the value of numIterations that your program observes may be any value greater than or equal to 3. Note that your program does not need to print out each of the random values that it generates. The steps to solve Question 2 are broken down as follows.
a. Implement a branching condition that increases the variable counter by 1 if val is larger than 0.5 1
b. Add a loop around the code created in Part a that continues until counter equals 3.
c. Use the variable numlterations to count how many times your loop iterates.
Answers
Answer:
ok where do i put anwaer?
Explanation:
Write a function input_poly(ptr1) that reads in two polynomials at a time with coefficient and exponent from a file cp7_in.txt. The file will contain 2n polynomials, where n is an integer that is 10 or less. Space for the polynomial will be allocated in run time and there is no limit to the size of the polynomial, e..g the first two lines of the file is
Answers
Answer:
try this
Explanation:
#include<stdio.h>
#include<malloc.h>
typedef struct poly{ double coff;
int pow;
struct poly *link; }SL;
void create(SL **head)
{
*head=NULL;
}
//Insertion
void ins_beg(SL ** head, double c, int pw)
{
SL *ptr;
ptr=(SL *)malloc(sizeof(SL));
ptr->coff=c;
ptr->pow=pw;
ptr->link=*head;
*head=ptr;
}
void trav(SL **head)
{
SL *ptr;
ptr=*head;
printf("\n\t Cofficient Exponent\n");
while(ptr!=NULL)
{ printf("\t\t%3.2f \t%d\n",ptr->coff, ptr->pow);
ptr=ptr->link;
}
}
//addition of polynomial............
void mult(SL *pl1, SL *pl2, SL **res)
{
SL trav1, trav2, ptr, new1,*loc;
int x,y;
trav1=*pl1;
while(trav1!=NULL)
{
trav2=*pl2;
while(trav2!=NULL)
{
x=(trav1->coff)*(trav2->coff);
y=(trav1->pow)+(trav2->pow);
//printf("\t%d\t%d\n",x,y);
if(*res==NULL)
{
new1=(SL *)malloc(sizeof(SL));
new1->coff=x;
new1->pow=y;
new1->link=NULL;
*res=new1;
}
else
{
ptr=*res;
while((y<ptr->pow)&&(ptr->link!=NULL))
{
loc=ptr;
ptr=ptr->link;
}
if(y==ptr->pow)
ptr->coff=ptr->coff+x;
else
{
if(ptr->link!=NULL)
{
new1=(SL *)malloc(sizeof(SL));
new1->coff=x;
new1->pow=y;
loc->link=new1;
new1->link=ptr;
}
else
{
new1=(SL *)malloc(sizeof(SL));
new1->coff=x;
new1->pow=y;
ptr->link=new1;
new1->link=NULL;
}
}
}
trav2=trav2->link;
}
trav1=trav1->link;
}
}
//...addition..............
void add(SL *pl1, SL *pl2)
{
SL trav1, ptr, *new1,*loc; trav1=*pl1;
while(trav1!=NULL)
{
loc=ptr=*pl2;
while((trav1->pow<ptr->pow)&&(ptr->link!=NULL))
{
loc=ptr; ptr=ptr->link;
}
if(loc==ptr)
{
new1=(SL *)malloc(sizeof(SL));
new1->coff=trav1->coff;
new1->pow=trav1->pow;
new1->link=*pl2;
*pl2=new1;
}
else
if(trav1->pow==ptr->pow)
{
ptr->coff=ptr->coff+trav1->coff;
//ptr->pow=ptr->pow+trav1->pow;
}
else
if(ptr->link!=NULL)
{
new1=(SL *)malloc(sizeof(SL));
new1->coff=trav1->coff;
new1->pow=trav1->pow;
new1->link=ptr;
loc->link=new1;
}
else
{
new1=(SL *)malloc(sizeof(SL));
new1->coff=trav1->coff;
new1->pow=trav1->pow;
new1->link=NULL;
ptr->link=new1;
}
trav1=trav1->link;
}
}
int main()
{
SL first, sec, *res;
create(&first);
ins_beg(&first,10.25,0);
ins_beg(&first,4,1);
ins_beg(&first,5,2);
ins_beg(&first,4,4);
printf("\nFirst Polinomial:\n");
trav(&first);
create(&sec);
ins_beg(&sec,11,0);
ins_beg(&sec,6,1);
ins_beg(&sec,4,2);
ins_beg(&sec,3,3);
printf("\nSecond Polinomial:\n");
trav(&sec);
create(&res);
printf("\nMultiplication of two Polinomial:\n");
mult(&first,&sec,&res);
trav(&res);
printf("\nAddition of two Polinomial:\n");
add(&first,&sec);
trav(&sec);
//trav(&first);
return 0;
}
search for five ms excel terms
Answers
Answer:
work book, work sheet, cell, columns and rows
I am a bunch of large LANS spread out over several physical locations. Who am I?
Answers
Answer:
You're WAN
Explanation:
Wide Area Network
PLEASE HELP ME ASAP ITS IMPORTANT
Answers
Which security measure provides protection from IP spoofing?
A ______ provides protection from IP spoofing.
PLEASE HELP I need to finish 2 assignments to pass this school year pleasee im giving my only 30 points please
Answers
Answer:
An SSL also provides protection from IP spoofing.
In numerical methods, one source of error occurs when we use an approximation for a mathematical expression that would otherwise be too costly to compute in terms of run-time or memory resources. One routine example is the approximation of infinite series by a finite series that mostly captures the important behavior of the infinite series.
In this problem you will implement an approximation to the exp(x) as represented by the following infinite series,
exp(x) = Infinity n= 0 xn/xn!
Your approximation will be a truncated finite series with N + 1 terms,
exp(x, N) = Infinityn n = 0 xn/xn!
For the first part of this problem, you are given a random real number x and will investigate how well a finite series expansion for exp(x) approximates the infinite series.
Compute exp(x) using a finite series approximation with N E [0, 9] N (i.e. is an integer).
Save the 10 floating point values from your approximation in a numpy array named exp_approx. exp_approx should be of shape (10,) and should be ordered with increasing N (i.e. the first entry of exp_approx should correspond to exp(x, N) when N = 0 and the last entry when N = 9).
Answers
Answer:
The function in Python is as follows:
import math
import numpy as np
def exp(x):
mylist = []
for n in range(10):
num = (x**n)/(math.factorial(n))
mylist.append([num])
exp_approx = np.asarray(mylist)
sum = 0
for num in exp_approx:
sum+=num
return sum
Explanation:
The imports the python math module
import math
The imports the python numpy module
import numpy as np
The function begins here
def exp(x):
This creates an empty list
mylist = []
This iterates from 0 to 9
for n in range(10):
This calculates each term of the series
num = (x**n)/(math.factorial(n))
This appends the term to list, mylist
mylist.append([num])
This appends all elements of mylist to numpy array, exp_approx
exp_approx = np.asarray(mylist)
This initializes the sum of the series to 0
sum = 0
This iterates through exp_approx
for num in exp_approx:
This adds all terms of the series
sum+=num
This returns the calculated sum
return sum
Write a program that reads in a text file, infile.txt, and prints out all the lines in the file to the screen until it encounters a line with fewer than 4 characters. Once it finds a short line (one with fewer than 4 characters), the program stops. Your program must use readline() to read one line at a time. For your testing you should create a file named infile.txt. Only upload your Python program, I will create my own infile.txt using break
Answers
Answer:
Explanation:
f=open("infile.txt","r")
flag=True
while(flag):
s=f.readline().strip()
if(len(s)>=4):
print(s)
else:
flag=False
List any two programs that are required to play multimedia products
List any two programs that are required to create multimedia products
Answers
Answer:
the two programs to play multimedia products are;windows media player and VLC media player and the two programs to create multimedia products are;photoshop and PowerPoint
Which principle of layout design is shown below
Answers
1. Tracy is studying to become an esthetician. Give three reasons why she needs to have a thorough
understanding of facial machines.
Answers
write a object oriented c++ program
Answers
Answer:
I don't know how to code C++
Explanation:
Write an interface called Shape, inside, there is a method double area(); write a class called Box which implements the Shape. In Box, there are two data members: a double called length, and a double called width. Also implements constructor, and the method area() which calculates the area by multiplying the length and width. Then write a Tester class, which has a main method and creates a box object and displays the area.
Answers
Answer:
Explanation:
The following code is written in Java. It contains the interface Shape, the class Box, and a tester class called Brainly with the main method. Box implements the Shape interface and contains, the instance variables, the constructor which takes in the inputs for length and width, getter methods for length and width, and the defines the area() method from the interface. Then the object is created within the Brainly tester class' main method and the area() method is called on that object. Output can be seen in the image attached below. Due to technical difficulties, I have added the code as a txt file below.
When determining the statement of purpose for a database design, what is the most important question to ask?
O Who will use the database?
O Should I use the Report Wizard?
O How many copies should I print?
O How many tables will be in the database?
Answers
Answer: A. Who will use the database?
Explanation:
When determining the statement of purpose for a database design,the most important question to ask is Who will use the database?
What is the purpose of statement of purpose for a database ?Statement of purpose in a data base is very essential to know more about the database, this is why it is important to ask the question Who will use the database?
This question help the programmer to know the kind of data that will be running at the database so as make sure the database serve the required purpose.
Therefore option A is correct.
Read more about database at:
https://brainly.com/question/518894
#SPJ9
Plz hurry it’s timed
Answers
You have configured a LAN with 25 workstations, three network printers, and two servers. The workstations and printers will have dynamically assigned IP addresses, and the printers always need to have the same IP address assigned. The servers will have static IP addresses. What should you install on one of the servers, and what are some of the configuration options
Answers
Answer:
install and configure on the server DHCP (Dynamic Host Configuration Protocol)
Explanation:
In this scenario, you should install and configure on the server DHCP (Dynamic Host Configuration Protocol), this protocol automatically assigns each individual PC a unique IP address and DNS server information. This protocol has various configuration options such as being able to set a range for the IP addresses so that they can be used by different devices in the system. It also allows you to directly set the subnet and passage gateway so that all of the workstations can quickly communicate with one another and quickly be targeted by the administration.
1) Create a class called Villain. Specifically, a Villain has the following fields: .name (String)
a number of evil plans (int) In addition, a Villain has the following methods: • a constructor that accepts an argument for each of the fields . a copy constructor
an equals method, which checks/returns whether all the fields are the same
a toString method
2) Create a class called Crazy Villain, which inherits from Villain. Specifically, a Crazy Villain has the following additional fields:
a crazy laughter (String)
a crazy idea (String In addition, write code for the following Crazy Villain methods:
a constructor that accepts an argument for each of the fields
a toString method that overrides the Villain toString method, in order to include the additional fields You do not need to instantiate/demo Villain or Crazy Villain objects.
Answers
Answer:
Explanation:
The following code is written in Java and creates both of the classes as requested with their variables and methods as needed. The crazyVillain class extends the Villain class and implements and overrides the needed variables and methods. Due to technical reasons, I have added the code as a txt file below.
In a spreadsheet what does the following symbol mean?
$
Answers
Answer:
$ = dollar sign
Explanation:
In a spreadsheet, the $ symbol is the symbol of the dollar. The dollar is the currency of the United States.
What is currency?Currency is a form of payment for goods and services. In a nutshell, it is money in the form of paper and coins that is usually issued by a government and is generally accepted as a form of payment at face value.
Currency exchange rates differ between businesses because each one distorts the interbank rate to maximize profits. We encounter numerous competitors who post interbank rates internet as bait to attract new customers, but once the customers are onboard, they drastically change the rate, typically not in the customers' favor.
Therefore, the $ symbol represents the dollar in a spreadsheet. The US dollar is the country's currency.
To learn more about a dollar, refer to the below link:
https://brainly.com/question/23899116
#SPJ2
Who is MrBeast?
Answer the question correctly and get 10 points!
Answers
Answer: MrBeast is a y0utuber who has lots of money
Explanation:
Answer:
He is a You tuber who likes to donate do stunts and best of all spend money.
It's like he never runs out of money.
Explanation:
Explain the IT vendor selection and management processes
Answers
Answer:
The vendor management process includes a number of different activities, such as: Selecting vendors. The vendor selection process includes researching and sourcing suitable vendors and seeking quotes via requests for quotation (RFQs) and requests for proposal (RFPs), as well as shortlisting and selecting vendors. hope it helps
Complete the statement below using the correct term.
One recurring problem in networking is finding that users have used a hub or a switch to circumvent a
________
Answers
Answer:
HURRY
Dr. Khan works for the marketing department of a company that manufactures mechanical toy dogs. Dr. Khan has been asked to assess the effectiveness of a new advertising campaign that is designed to be most persuasive to people with a certain personality profile. She brought four groups of participants to the lab to watch the video advertisements and to measure the likelihood that they would purchase the toy, both before and after watching the ad. The results of Dr. Khan’s study are presented below.
Part A
Explain how each of the following concepts applies to Dr. Khan’s research.
Survey
Dependent variable
Big Five theory of personality
Part B
Explain the limitations of Dr. Khan’s study based on the research method used.
Explain what Dr. Khan’s research hypothesis most likely was.
Part C
Use the graph to answer the following questions.
How did the trait of agreeableness affect how people responded to the new ad campaign?
How did the trait of conscientiousness affect how people responded to the new ad campaign?
How should work be allocated to the team in a Scrum project?
Answers
Answer:
In a Scrum project, the work or the tasks are not allotted specifically. The Scrum Master is not allowed to assign tasks to the team members under any circumstance. Once the client provides the details regarding their requirements in detail, the tasks are distributed based on the expertise and skills of the employee.
Explanation:
Why is it important to isolate evidence-containing devices from the internet?
To save the battery
To hide their location
Devices can be remotely locked or wiped if connected
It is not important to isolate the devices
Answers
Answer:
C.
Devices can be remotely locked or wiped if connected
Explanation:
why the internet is not considered a mass medium in Africa
Answers
“Mass media,” therefore, would be that content created by a few and copied to the many — a large circulation newspaper, for example, or a network television or radio program.
The internet’s content is anything but “mass” in that regard — there is mass media content on it, to be sure, but there is also a panoply of content created by many for dissemination to many — or the few who are attracted by the content created by a certain few, or a certain individual. The reasons why there is not an internet infrastructure like in other regions is because in Africa people have low levels of computer literacy, there is poor infrastructures in power supply and urbanism in general, and Internet services are offered only at a high cost. Hope this helps!
Answer:
the reason why internet not considered as a mass medium is probably because most of the African are not educated and civilized, thereby making them not common to the usage of the internet.
Who first demonstrated the computer mouse?
O Microsoft
O Alan Turing
O Douglas Engelbart
O Apple, Inc.
FAST PLEASEEE THANK YOUUU
Answers
Answer:
C. Douglas Engelbart
Explanation:
Answer: C
Explanation: